In the beginning of September 2013, the CryptoLocker malware variant appeared in the wild, spread exclusively by the infamous P2P ZeuS (aka Gameover ZeuS) malware. CryptoLocker had a simple purpose: to act as ransomware, encrypting important files such as images and documents, and then asking the victim for money to unlock the files.

Image source: Ars Technica
In collaboration with FireEye, InTELL analysts at Fox-IT worked on the investigation. By the end of 2013, certain groups that were focused on online banking fraud, were moving to less risky attacks, such as ransomware, click fraud, and crypto coin mining. All of these attack types pose lower risk to the criminals compared to online banking attacks. P2P ZeuS was one of these groups.
US Law Enforcement led a joint operation from the 30th of May 2014, leading to a long term disruption of both P2P Zeus and CryptoLocker. A detailed description of the operation is available here.
CryptoLocker used AES symmetric cryptography to encrypt the files and encrypted the AES key with an RSA-2048 bit public key generated on the server side of CryptoLocker. For each infection a new RSA asymmetric key pair was generated on the CryptoLocker server. This rendered files impossible to recover for CryptoLocker victims on their own. To recover files, the malware offered victims the option to purchase the required RSA-2048 private key. The CryptoLocker authors began charging victims 100 USD in September 2013 to recover their files, and by May 2014, were charging victims 500 USD for recovery.
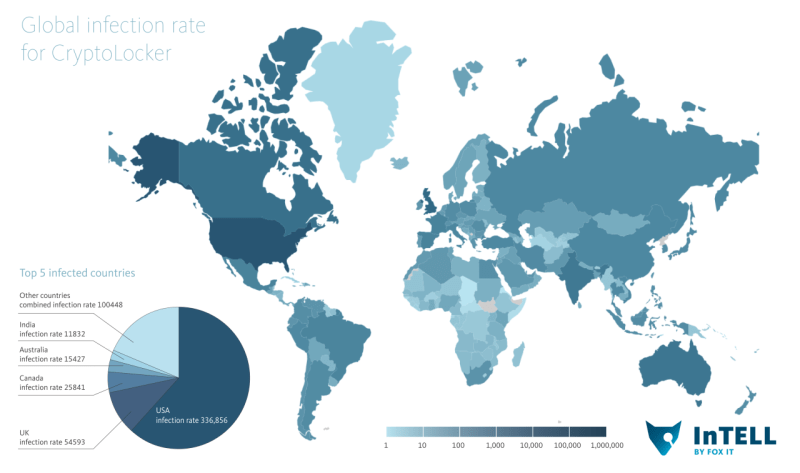
Not every computer infected with P2P ZeuS malware became infected with CryptoLocker. The reason for this is that CryptoLocker ran on victim machines alongside P2P ZeuS malware, which was used to commit financial fraud. In order for P2P ZeuS to be successful, a victim had to remain unaware that his/her system was compromised. Therefore, only a handful of P2P ZeuS botnets within the full P2P ZeuS network installed CryptoLocker. From September 2013 through May 2014, over half a million (545,146) infections occurred. This is much less than the amount of infections of P2P ZeuS over the same period.
Of the botnets distributing CryptoLocker, infections were mostly limited to victims located in the US, Canada, UK and Australia. These regions were most likely selected for their use of English as the primary language. This is shown in the heat map below – with over 60% of the CryptoLocker infections located in the US.
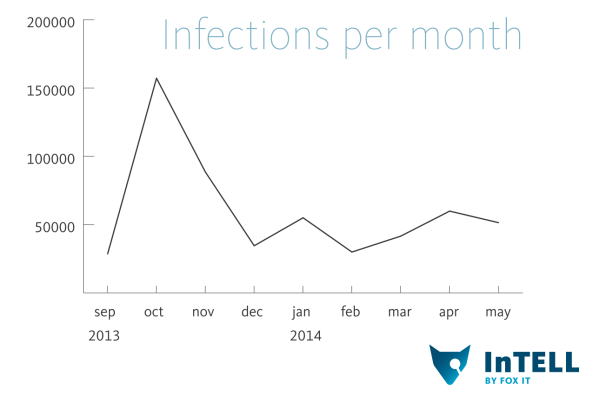
While CryptoLocker infections started in the beginning of September 2013, the largest number of infections in one month occurred during October 2013, with over 155000 systems affected worldwide. This accounts for nearly 29% of all infections between September and May 2014. After October 2013 the rates dropped, but still steadily pacing at around 50,000 infections per month.
The CryptoLocker infrastructure was separate from the P2P ZeuS infrastructure. It used a fast-flux network offered by a bulletproof hoster and a service hidden in the TOR network. These two channels were terminated on a proxy system that lead directly to the backend system, allowing victims to pay the ransom even though the fast flux network experienced various disruptions by security researchers.
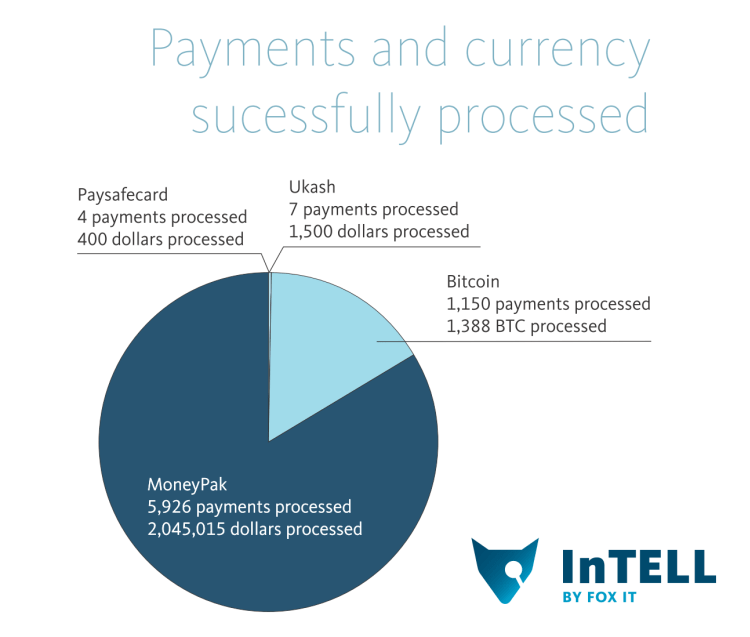
The majority of victim payments to CryptoLocker were processed through Moneypak, but also a considerable amount of money was paid through the use of Bitcoins. A new Bitcoin address was created for each infection, making it harder for researchers to track and easier for CryptoLocker operators to distinguish transactions. In total, over 1400 Bitcoins (1407.24575477 BTC, around 700,000 USD in current exchange rates) were received. That is more than the 1388 BTC the malware requested, apparently some victims tried to transfer partial amounts. Unfortunately for them these lower amounts were lost for them and they added a small bonus for the criminals. A small number of early payments were received via Paysafecard and Ukash. In total, the amount of money made during the 9 month CryptoLocker operation was around 3 million USD. This accounts for the fluctuating Bitcoin exchange rate over time.
In the end, 1.3% of victims paid a CryptoLocker ransom, therefore, a large amount of victims likely permanently lost files due to this attack. Fox-IT InTELL and FireEye provide a free service to victims, to recover the private keys associated to CryptoLocker infections. This was announced on August 6 2014, in this press release. This gives CryptoLocker victims the ability to recover their files and restore the contents.
A big thank you to Kyrus tech for their tool Cryptounlocker. And finally we wish to thank Surfright for their assistance by providing encrypted files they generated using CryptoLocker.
Michael Sandee
Links:
http://www.fireeye.com/
http://www.fox-it.com/
http://www.foxintell.com
https://www.decryptcryptolocker.com/
http://www.fbi.gov/news/pressrel/press-releases/u.s.-leads-multi-national-action-against-gameover-zeus-botnet-and-cryptolocker-ransomware-charges-botnet-administrator
http://www.kyrus-tech.com/cryptolocker-decryption-engine/
http://www.surfright.nl/en
http://arstechnica.com/security/2013/10/youre-infected-if-you-want-to-see-your-data-again-pay-us-300-in-bitcoins/
http://www.fireeye.com/news-events/press-releases/read/fireeye-and-fox-it-announce-new-service-to-help-cryptolocker-victims
Please fix your link at “A detailed description of the operation is available here.”
It has to be a lowercase ‘c’ in the Url for the cryptolocker part, see the correct one here:
http://www.fbi.gov/news/pressrel/press-releases/u.s.-leads-multi-national-action-against-gameover-zeus-botnet-and-cryptolocker-ransomware-charges-botnet-administrator
My computer was infected on August 6, 2014. I tried to upload an encrypted file on decrpytcryptolocker.com but received the following message:
“The file does not seem to be infected by CryptoLocker. Please submit a CryptoLocker infected file.”
Any ideas on what is happening here?
I have the same issue – none seems to be able to help.
Hi!
If you are receiving that error it is because probably you are not infected with CryptoLocker. This service provides support only for systems infected with CryptoLocker before the summer of 2014. Unfortunately, if you have been infected after that time and you see that error in the web page, it means that this service cannot help you. In fact, if your machine was infected after that time you are not infected with CryptoLocker but with another ransomware family like Cryptowall, TorrentLocker, etc.
I hope this helps!
Jose
I recently found that my âcryptolockedâ files were actually infected by an imitation cryptolocker. A solution for the imitation version can be found here:
http://www.bleepingcomputer.com/forums/t/547708/torrentlocker-ransomware-cracked-and-decrypter-has-been-made/
Good luck!
Hi Craig,
I recently found that my “cryptolocked” files were actually infected by an imitation cryptolocker. A solution for the imitation version can be found here:
http://www.bleepingcomputer.com/forums/t/547708/torrentlocker-ransomware-cracked-and-decrypter-has-been-made/
Good luck!
Thanks for the article and the link. Using Vista in the USA I attempted to upload to the link. Numerous attempts over the last two weeks have been unsuccessful. Is the site down? …overloaded? I have the ransomware Cryptowall. Thanks for your followup.
im getting “The file does not seem to be infected by CryptoLocker. Please submit a CryptoLocker infected file.” please help
same as Frank- what can I do????????????????
Jon