A month ago Fox-IT and FireEye announced the DecryptCryptoLocker service, which provides free private keys to victims of the CryptoLocker Malware. We decided not only to share the information with victims for free, but also provide a website that provides the right key to victims, saving them a lot of time and effort. For each request the website needs to do comparisons to over half a million private keys to obtain the right one. This blog and the accompanying one from FireEye serves as an update on CryptoLocker and the DecryptCryptoLocker service.
Reactions
We’ve got a lot of reactions, hundreds of inquiries and thank you notes, and tens of thousands of social media interactions. Steve Belleguelle, system administrator for multiple customers, wrote “Just a short message to say thank you so much for the work in obtaining the CryptoLocker keys database and then providing the DecryptCryptoLocker website. One of my customers ‘lost’ many thousands of files due to this malware and we have now been able to recover most of them.” For us that reaction alone makes it worth the effort, but Steve is not alone: up until last week we were able to provide 2900 keys to victims, and dozens of keys are still being provided on a daily basis. For that reason we decided to keep the DecryptCryptoLocker website running for several months. If you know a victim, point them to it.
Update on CryptoLocker
Most of the operators behind P2P ZeuS and CryptoLocker have not been seen since the operation against this group and their infrastructure, however this does not mean that the threat has gone away. The past months have seen a lot of fluidity, caused by new players trying to enter this space and existing customers of the P2P ZeuS group looking for new solutions for their crimeware needs.
Parts of the inject code have reappeared in other botnets, we are tracking new malware variants being developed which appear to re-use or build upon parts of P2P Zeus and there is an upsurge activity from Gozi, Bugat and other existing malware variants. This means some of the high profile customers of P2P Zeus are looking for a new custom piece of malware while others customers simply joined other existing operations like Gozi.
The fact that the CryptoLocker malware netted the P2P Zeus group significant income has also lead to renewed interest in ransomware as a way to make money and copycat malware using the same approach have now appeared, an example being Cryptowall – which has even copied part of the name.
Some numbers
When we started the project, we could only guess how many people we would be able to help. Now, after a month we can do a first assessment.
Please note that these statistics are not in any way correlated to personal identifiable information; and that PII was used for nothing else than delivering the private keys.
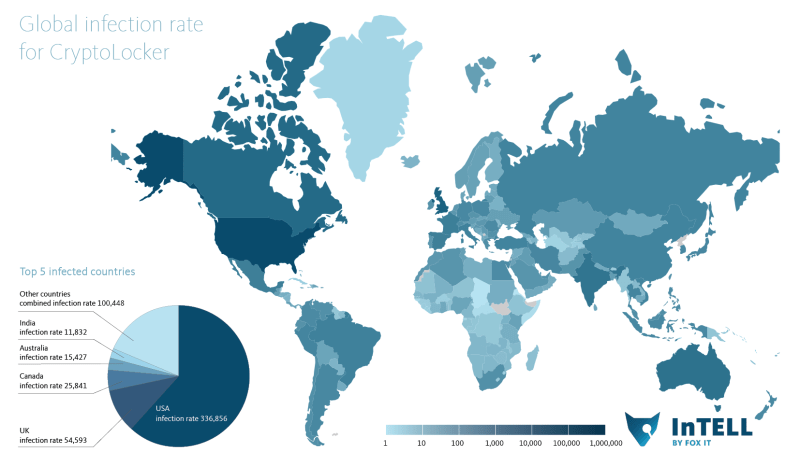
The infection rate as mentioned in the original blog post is shown below:
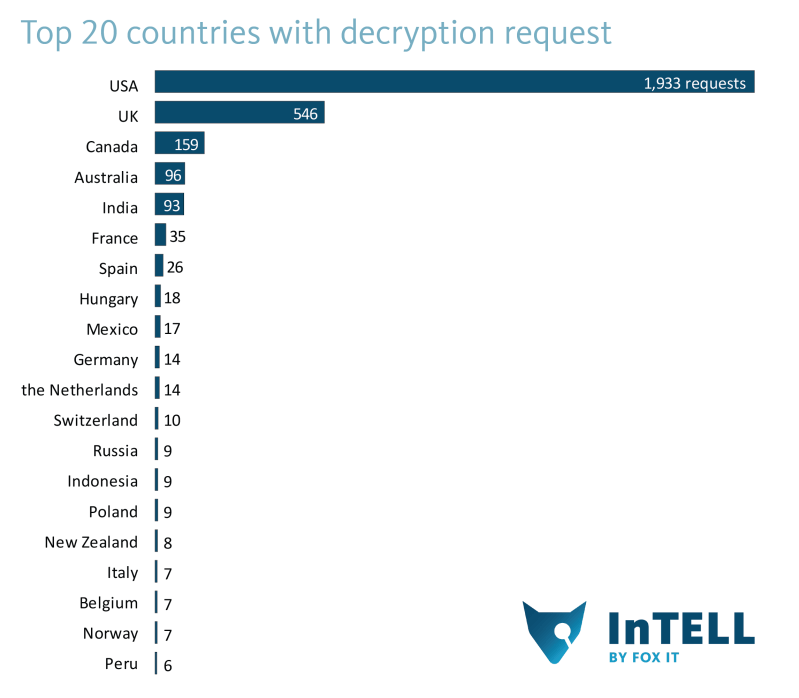
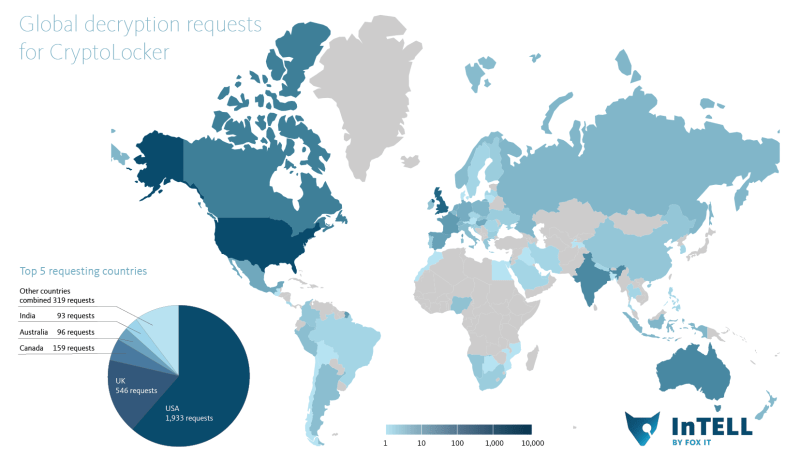
If we compare that to the decryption requests, we can see the data correlates. Indeed the top countries requests are made from, are countries where English is a major language.
The total number of valid decryption requests is 2900. An interesting fact is that in the UK, relatively more victims have requested their keys than in the US – more than in all other large countries to be precise. Only some very small countries with a handful of infections showed greater ratios, which can be attributed to too low statistical sample sizes.
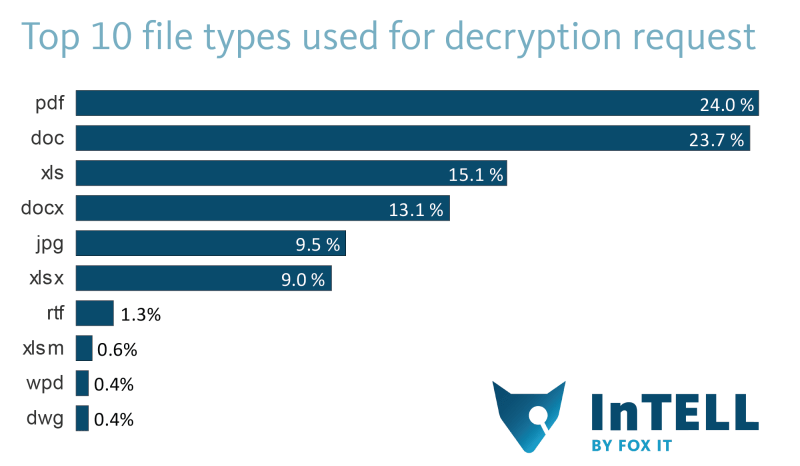
The type of files that were offered for private key matching show some interesting things too.
Although this is not necessarily a representation of the actual files being encrypted with malware, one can imagine that a .dwg file (a CAD file) might represent a lot of value to the victim, in terms of specialist hours spent on working on the file.
Feedback and other ransomware victim solutions
We try to answer every question we’re asked via e-mail or social media. Due to the overwhelming amount of feedback a reaction might have taken some time. The most asked question was from victims of other ransomware: will we be able to provide a solution for CryptoWall, Synolocker, CryptoLocker V2 or others? Unfortunately we don’t offer decryption keys for these ransomwares. It is unlikely we will provide something for that anytime soon.
Conclusion
The DecryptCryptoLocker service has been able to help thousands, and will be continued for several months, hopefully helping more victims reclaiming their files. While the original CryptoLocker malware is not used anymore, criminals though seem encouraged by its success and many more families of ransomware are now seen in the wild.
Great Job Fox and all for Free
Thank you Fox-IT & FireEye for this service, it has helped one of our customers greatly.
10 mths ago we advised them not to throw the HDD away after they were hijacked. With your superb service we were able to return all their files to them a couple of weeks ago.
We now have one very happy customer, thank you to all.
TM.
help … can you help me to remove CryptoLocker
“Unsuccessful loading key : RSA key format is not supported.” Any chance of sending me an email with exact commands to make sure this isn’t user error? I’ve been unable to use the provided key on any files. Thank you!
I cannot upload any files. It just stays on that page and does not do anything.
HELP!
For me it didn’t work, after a successful decryption I still couldn’t open the file
is there any cure for cryptowall?
Sorry to say this, but the service sucks!
A client had an infection and i did try to use decryptcryptolocker but without any succes because the service doesn’t accept/recognised the encrypted files.
I did try so send an email, but it couldn’t be delivered.. Then i search the websites to find any contact details, posted a message in their blog (Your comment is awaiting moderation. ), etc. etc.
Still no response, only a message from some company wizzkidd who says i should use the contact details on their page… WELL THERE ARE NO CONTACT DETAILS ON THE PAGE
Is there someone from FOX IT who is willing to help?????
it’s a free service RWS, quit acting as a spoiled little child. If your file does not get recognized it is probably a newer virus for which they have no key for as of yet.
Deal with it, the files are lost. The only thing you can do is restore a back-up.
Website does not recognize my encrypted files! I try some files but it tells files are invalid. What should I do?
Hello to all, the virus that has infected my files generated an extension .svcwodk. anyone can help me?
got infected few days ago and service doesn’t work
when i up load the file i get the following message please assist?
“The file does not seem to be infected by CryptoLocker. Please submit a CryptoLocker infected file.”
JULIO.XLSX.jrwgsza